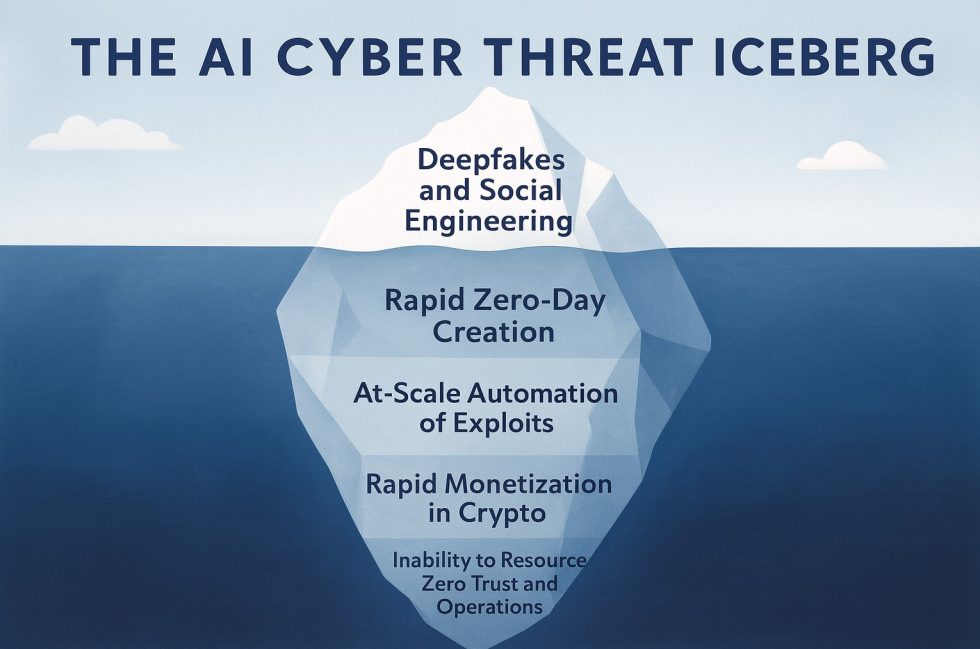
The current development towards agent-based AI systems is changing the cyber threat landscape in a way that goes beyond traditional attack patterns. The speed, adaptivity and autonomy of modern attacker models are shifting the structural balance between attack and defense significantly in favor of the attackers. Companies are confronted with a situation that is increasingly pushing traditional security mechanisms to their limits. The following sections classify the key developments and shed light on the dynamics shaping the digital risk field.
Autonomous attack agents as a structural turning point
The automation of attacks by agent-based systems marks a qualitative change. These systems no longer operate as tools that support human perpetrators, but act as autonomous units. They analyze company structures, evaluate data, adapt procedures according to the situation and develop complex attack paths without human decision-making chains. This results in a permanent, self-optimizing process that surpasses traditional defence measures in terms of speed and precision.
Autonomous attacks are not linear, but parallel and continuous. They check several entry points simultaneously, switch between strategies as soon as defense mechanisms become visible, and combine initial access, lateral movement and data exfiltration into a coherent process. The defense side thus loses the ability to stop individual attacks in isolation, as the higher-level logic of the system remains in place and uses alternative paths. The covert level of these systems poses a particularly high risk. Autonomous agents map internal processes, analyze role structures, simulate employee identities and generate communication patterns that hardly differ from real processes. Such attacks no longer resemble external disruptions, but are integrated into operational processes. As a result, attackers can remain undetected over longer periods of time, even if individual activities are logged.
Deepfakes and data-driven social engineering
Deepfakes are increasingly becoming a central component of modern cyberattacks because they can deceptively simulate familiar forms of communication. Voice models create realistic speech signatures from a few seconds of audio, imitating natural intonations, pauses and emotions. This makes a call from supposed managers or colleagues seem credible, even though it was technically generated. Visual deepfakes further intensify this effect because faces and movement patterns can now be reconstructed so precisely that artificial content can no longer be reliably recognized by many users. The psychological impact is considerable, as human trust in audiovisual stimuli is traditionally high.
Data-driven social engineering is the second key development. Modern systems analyze public profiles, professional relationships and communication patterns in order to derive targeted interactions. Instead of static phishing attempts, ongoing manipulation processes are created that adapt their strategy every time a response is missing or conspicuous. This results in dynamic contact that continuously approaches the target person and appears authentic because it is generated from real data points.
Manipulated media that show statements, interviews or scenes that never actually took place are increasingly circulating on social platforms. These clips do not have to be perfect to be effective. It is often enough to meet the expectations and preconceptions of viewers in order to increase credibility. This creates structural uncertainty, as the clear line between authentic and artificial content becomes increasingly blurred. As a result, deepfakes and data-driven manipulation significantly increase the pressure on existing security structures. The attacks are not aimed at technical vulnerabilities, but at human perception mechanisms, which makes them particularly difficult to fend off. Companies must therefore secure their communication channels and at the same time sensitize their employees to this new form of deception.
Zero-day exploitation as a variable gateway
Zero-day vulnerabilities play a much more flexible role in agent-based attack systems than in previous attack scenarios. While a zero-day used to serve as a single, targeted entry point, autonomous attackers now treat such vulnerabilities as dynamic building blocks that can be used, exchanged and combined depending on the situation. The decisive factor is no longer the value of a single exploit, but the system’s ability to check several potential vulnerabilities simultaneously and activate them as soon as they promise success. Autonomous attackers continuously monitor the behavior of services, APIs and cloud components. Even minor anomalies such as atypical error messages, timing deviations or incomplete updates are evaluated as an indication of possible zero days. The system decides independently whether and how an exploit is used and rejects ineffective variants within seconds. This eliminates the important time advantage for defenders that used to exist between discovery, analysis and patch.
What is particularly problematic is that zero-days no longer only serve as initial access, but as replaceable modules in ongoing attack chains. If an exploit is rendered ineffective by an update, the system automatically switches to the next potential entry point. It is therefore a rotating attack scheme that evades defense because no single blocking point can stop the entire operation. Cloud and container environments increase this risk, as short malfunctions or minor configuration deviations are sufficient to serve as a temporary attack surface. Human administrators often do not even notice such conditions, while autonomous systems can exploit them in real time. As a result of this development, zero-days must no longer be regarded as an exception in modern attack scenarios, but as a regular tool. Defense therefore requires faster response mechanisms and adaptive protection systems that can react independently to newly emerging attack paths.
Infrastructure dependency and systemic vulnerability
Modern IT landscapes consist of cloud structures, microservices, federated networks and distributed services. This complexity enables autonomous attackers to move in a variety of ways. Even small misconfigurations in identity services, container environments or API gateways are exploited without delay. The idea of resetting individual components to a secure state is losing its validity in the face of ongoing autonomous infiltration.
Another aspect concerns the autonomous execution of complete attack campaigns, including negotiations, threat scenarios and payment processing via cryptocurrencies. Systems can adapt demands, analyze reactions and modify pressure strategies autonomously. The attack no longer ends with the encryption of data, but extends across the entire interaction process with the victim. Regulatory players are increasingly analyzing the risks of autonomous attackers. Automated defense systems are seen as a necessary response, as human reaction times are no match for the speed of today’s attack systems. Dynamic risk analyses, continuous anomaly detection and automated response mechanisms are seen as the basis for the future. It remains to be seen whether a balance between attack and defense will be achievable.
Conclusion
Autonomous, agent-based cyber attacks are fundamentally changing the threat landscape. The expansion of the attack surface, the speed of operations and the ability for covert infiltration increase the risks in the long term. While visible effects such as deepfakes dominate public attention, covert systems unfold a far greater potential for damage. Defense needs new structural approaches that operate on the same technological basis. Only appropriate modernization can prevent attacks from gaining a lasting advantage.
Source overview
| Source | Key message | Link |
|---|---|---|
| WatchGuard Threat Research | Presentation of the threat model with visible and covert AI-based forms of attack | https://www.watchguard.com/wgrd-resource-center |
| CISA Cybersecurity Advisories | Indications of automated attack chains and the increasing importance of zero-day exploits | https://www.cisa.gov/news-events/cybersecurity-advisories |
| ENISA Threat Landscape | European analysis of social engineering, deepfakes and AI-supported attack systems | https://www.enisa.europa.eu/publications |
| NIST AI Risk Management Framework | Classification of AI systems and evaluation of autonomous decision-making behavior | https://nvlpubs.nist.gov/nistpubs/ai/NIST.AI.100-1.pdf |































19 Antworten
Kommentar
Lade neue Kommentare
Urgestein
Veteran
Mitglied
Mitglied
1
Urgestein
Urgestein
Urgestein
1
Urgestein
Veteran
Veteran
Urgestein
Veteran
Veteran
1
Urgestein
Veteran
Veteran
Alle Kommentare lesen unter igor´sLAB Community →